
Why a Checklist Won’t Ensure CMMC Readiness
This CMMC Myth Could Cost You
Many organizations believe they are CMMC compliant simply because they have completed a checklist. Policies may be drafted, forms filled out, and a few security controls implemented, but real readiness requires evidence that controls are implemented and functioning across your organization.
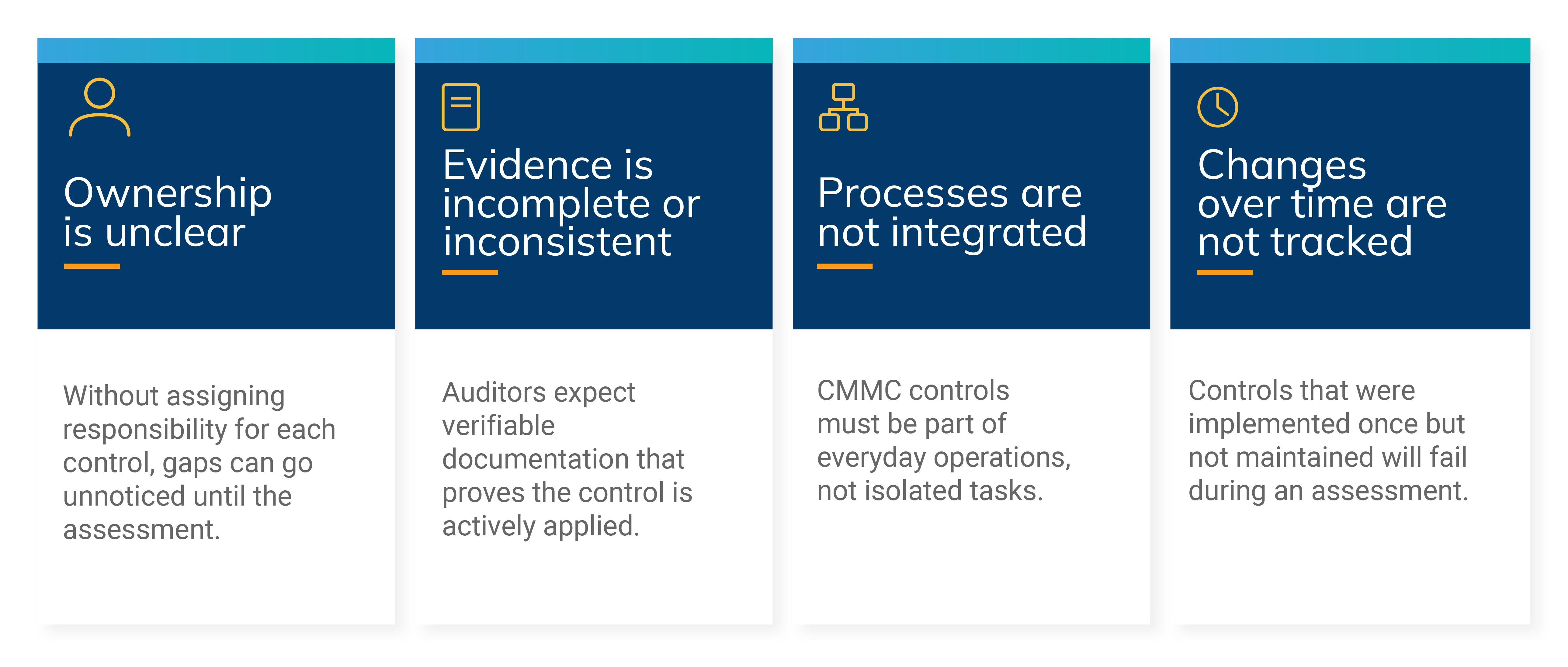
Auditors want proof that processes are executed consistently. Evidence can include system logs, access records, user activity, and other documentation demonstrating control effectiveness. A policy sitting on a shelf will not satisfy CMMC requirements.
Several Common Issues Prevent Checklists From Ensuring Readiness
Consider a contractor who checked off every item on a CMMC checklist without validating active implementation. During the official assessment, auditors discovered incomplete access logs and inconsistent incident response procedures. The contractor failed the assessment, delayed a contract award, and incurred extra costs to remediate deficiencies. Real-world examples like this highlight why checklists alone cannot guarantee readiness.
Treating readiness as a one-time effort often leads to costly surprises during assessments. Achieving true readiness requires a systematic approach that includes:
Conducting a thorough gap analysis to identify weaknesses
Assigning clear ownership for each control to ensure accountability
Collecting evidence of implementation that auditors can verify
Implementing continuous monitoring to maintain compliance over time
A readiness assessment identifies vulnerabilities, establishes accountability, and creates a roadmap to meet CMMC requirements. CMMC readiness is an investment in protecting your contracts, operations, and reputation. Organizations that understand this distinction are more likely to achieve compliance and maintain it long-term.
If you’re unsure where you stand or lost on where to begin, don’t leave it to chance. Contact our experts today to schedule a readiness assessment and take the first step toward full CMMC compliance.






